Printing on Windows from your own computer
Available printers
| Printer | Address | Duplex |
|---|---|---|
| Printer_A1 | \\printers.labs.wmi.amu.edu.pl\Printer_A1_PS |
Yes |
| Printer_B1L | \\printers.labs.wmi.amu.edu.pl\Printer_B1L_PS |
Yes |
| Printer_B1P | \\printers.labs.wmi.amu.edu.pl\Printer_B1P_PS |
Yes |
| Printer_B2L | \\printers.labs.wmi.amu.edu.pl\Printer_B2L_PS |
Yes |
| Printer_B2P | \\printers.labs.wmi.amu.edu.pl\Printer_B2P_PS |
Yes |
| Printer_B3L | \\printers.labs.wmi.amu.edu.pl\Printer_B3L_PS |
Yes |
| Printer_B3P | \\printers.labs.wmi.amu.edu.pl\Printer_B3P_PS |
Yes |
| Printer_B4P | \\printers.labs.wmi.amu.edu.pl\Printer_B4P_PS |
Yes |
| Printer_Lib | \\printers.labs.wmi.amu.edu.pl\Printer_Lib_PS |
Yes |
Guide
If your laptop is connected to the WMI network, you can print from it directly from Windows.
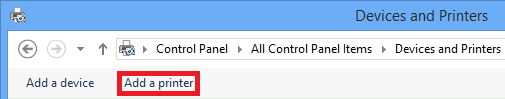
Open Control Panel -> Hardware and sound -> Devices and printers and click Add a printer:
Stop searching and click on *The printer I want isn't listed:

Select Select a shared printer by name and enter printer's address, for example
\\printers.labs.wmi.amu.edu.pl\Printer_A1_PS. Approve with Next button.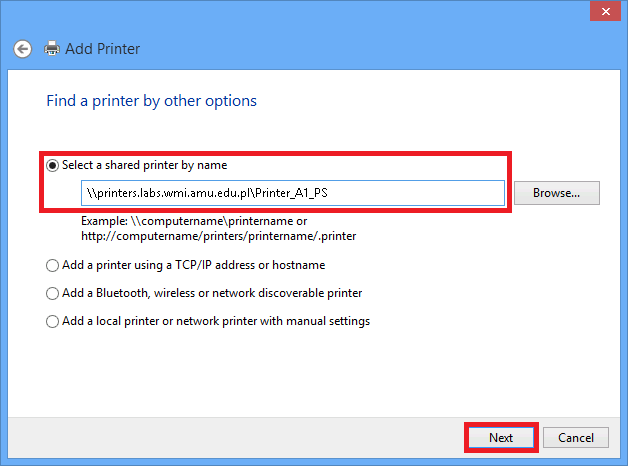
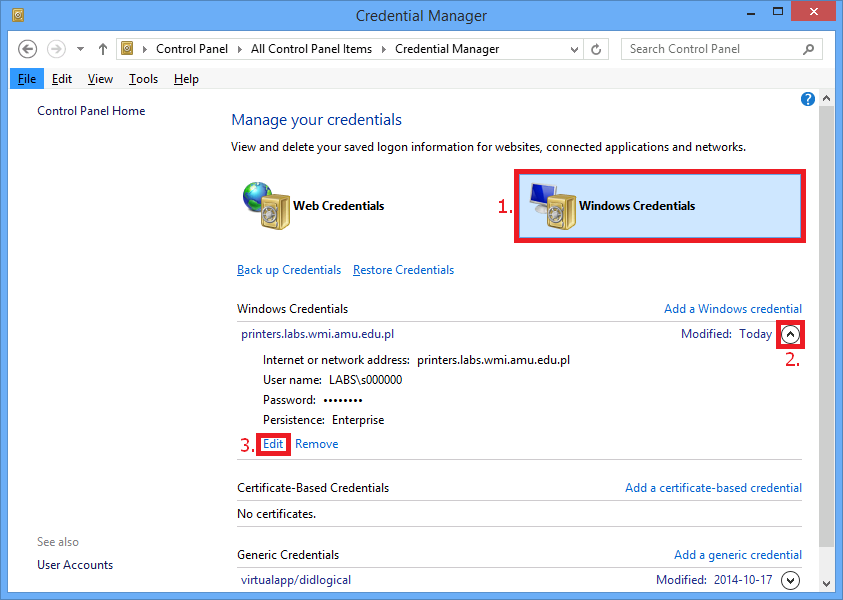
Enter login in
LABS\s000000format and LABS domain password, select password remembering: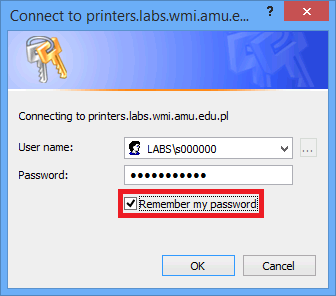
Finish installation procedure.
Due to the system's security against the PrintNightmare attack, there is a chance that the printer will not install properly on Windows.
To disable the protection, open CMD with administrator privileges and type the command below. The given command allows you to install drivers as a non-admin user.
reg add "HKEY_LOCAL_MACHINE\Software\Policies\Microsoft\Windows NT\Printers\PointAndPrint" /v RestrictDriverInstallationToAdministrators /t REG_DWORD /d 0 /fThis command makes your system vulnerable to PrintNightmare attack.
We do not take any responsiblilty for these actions. At the moment, we do not know a better way to solve this issue. After the installation of the printers, we recommend to re-enable protection by executing the following command:
reg add "HKEY_LOCAL_MACHINE\Software\Policies\Microsoft\Windows NT\Printers\PointAndPrint" /v RestrictDriverInstallationToAdministrators /t REG_DWORD /d 1 /f
 Computer Laboratories
Computer Laboratories